Takedown Requests
The Takedown Requests view tracks the status of requests to remove malicious content targeting your organization. When ShadowMap identifies phishing sites, fake applications, domain squatting, or other brand abuse, you can submit takedown requests and track their progress through resolution.
Overview
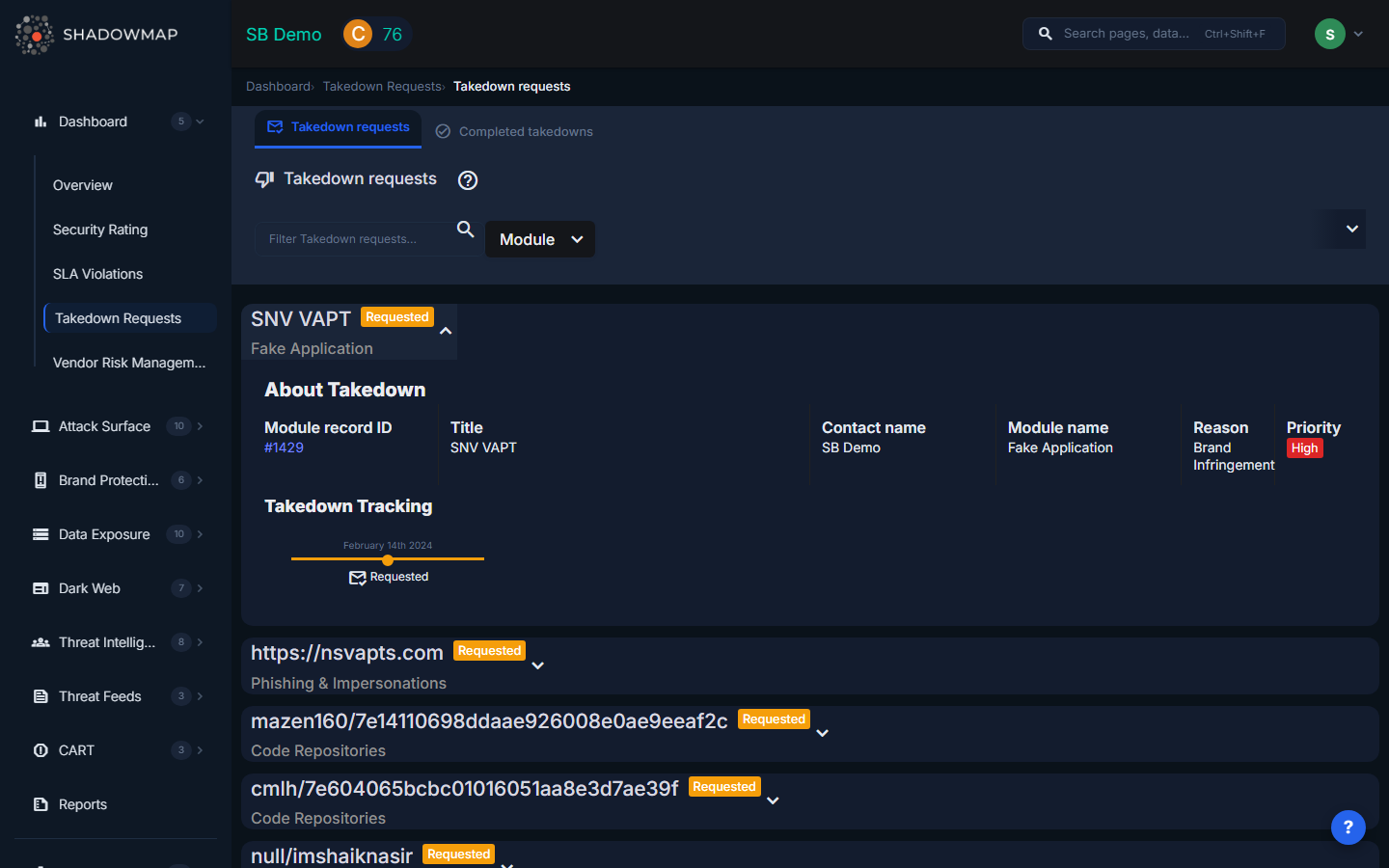
The page displays takedown requests as expandable accordion cards. Each card shows the takedown title, current status badge, and originating module. Cards can be expanded to reveal full details and a timeline view of the takedown's progress. A search bar and module filter allow narrowing the list.
Takedown Statuses
| Status | Description |
|---|---|
| Requested | The takedown has been submitted and is pending action by the hosting provider or registrar |
| In Progress | The hosting provider or registrar is processing the takedown request |
| Completed | The malicious content has been successfully removed |
| Failed | The takedown request was not successful -- the content remains online |
Takedown Card Details
Expanding a takedown card reveals:
| Field | Description |
|---|---|
| Module Record ID | Link to the original finding that triggered the takedown request |
| Title | Description of the malicious content being taken down |
| Contact Name | The customer or team member who submitted the request |
| Module Name | Which ShadowMap module the finding originated from |
| Reason | The stated reason for the takedown request |
| Priority | Priority level of the takedown (styled by severity) |
Takedown Timeline
Each takedown includes a visual timeline showing the progression through statuses with timestamps. This provides a clear audit trail of when the request was submitted, when the provider began processing, and when resolution occurred (or failed).
Submitting a Takedown
Takedown requests can be initiated from several ShadowMap modules:
| Module | What Gets Taken Down |
|---|---|
| Phishing & Impersonations | Phishing sites impersonating your brand, login pages, or web properties |
| Fake Applications | Counterfeit mobile apps on Google Play Store or Apple App Store |
| Domain Squatting | Domains registered to exploit your brand name |
| Social Media | Fake social media accounts impersonating your organization |
To submit a takedown:
- Navigate to the relevant finding in one of the modules above
- Click the Request Takedown action on the finding
- Fill in the takedown details (reason, priority, contact information)
- Submit the request
- Track progress from this Takedown Requests page
Filtering
| Filter | Description |
|---|---|
| Search | Free-text search across takedown titles and details |
| Module | Filter by originating module to see only phishing takedowns, fake app takedowns, etc. |
Recommended Workflow
- Submit takedowns promptly for confirmed malicious content -- delays increase user exposure
- Monitor In Progress status -- follow up with providers if requests stall
- Verify Completed takedowns -- confirm the malicious content is actually removed, not just redirected
- Re-submit Failed takedowns with additional evidence or through alternative channels
- Track resolution times to identify responsive and unresponsive hosting providers
- Document everything using the timeline for compliance and legal evidence
