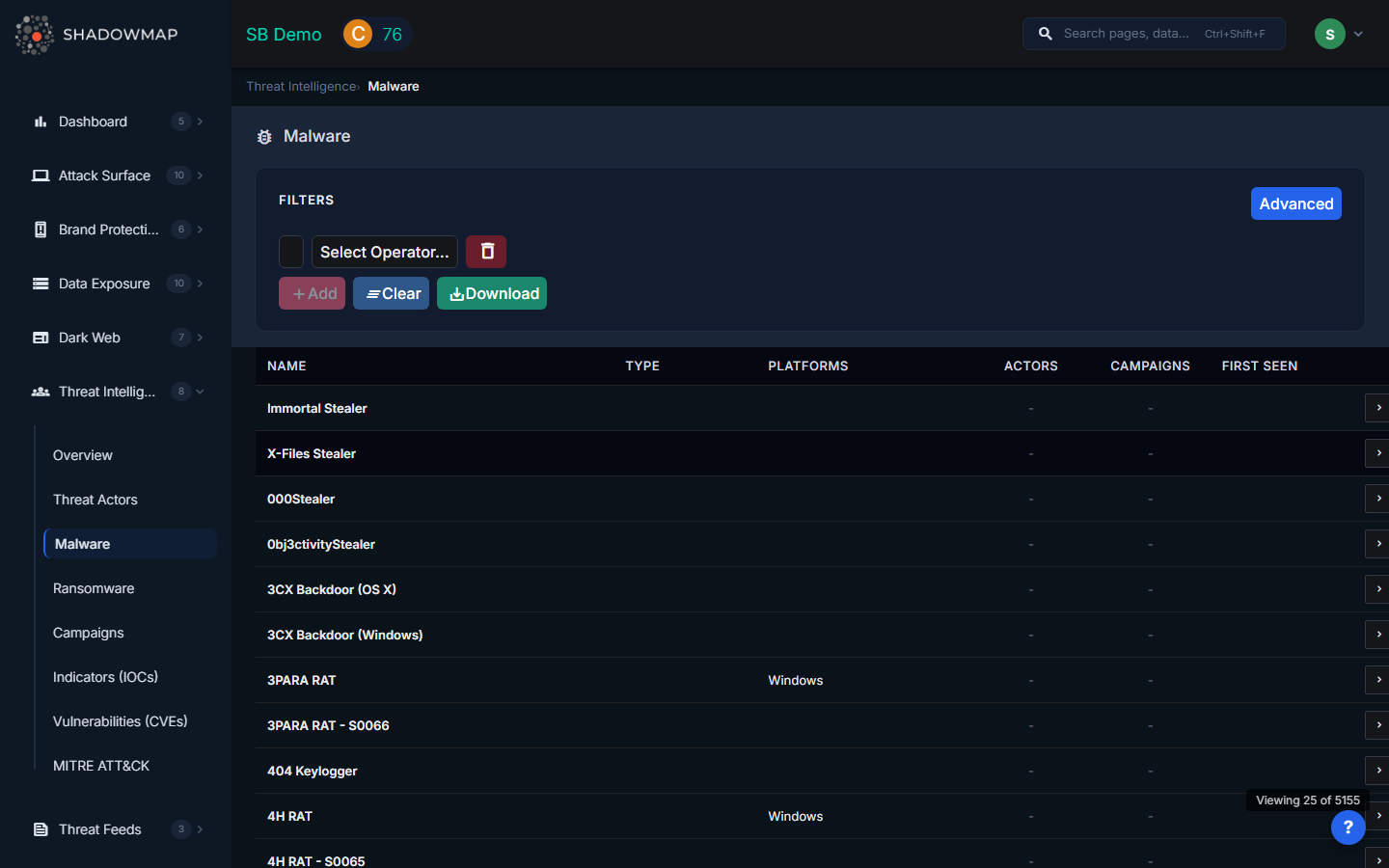
Malware
ShadowMap provides intelligence on malware families, including their type, target platforms, associated threat actors, and linked campaigns. This module helps security teams understand the tools used by adversaries so they can build appropriate detections and assess whether specific malware poses a risk to their environment.
Overview
Understanding the Data
The malware list displays the following columns:
| Column | Description |
|---|---|
| Name | Primary name of the malware family (e.g., Cobalt Strike, Emotet, TrickBot) |
| Type | Classification of the malware: RAT, backdoor, trojan, ransomware, worm, loader, info-stealer, rootkit, exploit kit, etc. (displayed as a tag) |
| Platforms | Operating systems and platforms the malware targets (shows top 3; e.g., Windows, Linux, macOS) |
| Actors | Count of threat actors known to use this malware family |
| Campaigns | Count of campaigns in which this malware has been observed |
| First Seen | Earliest known appearance of this malware in the wild |
Click any row to view the full malware profile, including detailed descriptions, full platform lists, all associated threat actors, campaigns, and related IOCs.
Filters
Use the filter bar to narrow the list:
| Filter | Options |
|---|---|
| Type | Filter by malware classification (RAT, backdoor, trojan, ransomware, etc.) |
| Platform | Filter by target platform (Windows, Linux, macOS, Android, etc.) |
| Search | Free-text search across malware names and descriptions |
Export
Click the export button to download the current filtered view as an Excel file. The export respects all applied filters and search terms.
How to Use Malware Intelligence
- Detection engineering -- Use malware names and types to search for corresponding YARA rules, Sigma rules, and Snort signatures in public repositories. Cross-reference with the IOC Search for associated indicators.
- Risk assessment -- Filter by platforms matching your environment. If your organization runs Windows servers and Linux workloads, filter for malware targeting those platforms and assess your detection coverage.
- Actor attribution -- Click through to associated threat actors to understand who uses this malware and whether they target your sector.
- Campaign tracking -- The campaigns count shows how actively the malware is being used. High campaign counts indicate widespread or ongoing use.
- Vendor evaluation -- When assessing EDR or AV products, use this list to verify whether your chosen solution detects the malware families most relevant to your threat landscape.
Understanding Malware Types
| Type | Description |
|---|---|
| RAT | Remote Access Trojan -- provides persistent remote control of the infected system |
| Backdoor | Provides unauthorized access, often simpler than a full RAT |
| Trojan | Disguises as legitimate software to deliver malicious payloads |
| Ransomware | Encrypts files and demands payment (also tracked in the dedicated Ransomware module) |
| Loader/Dropper | Downloads and executes additional malware payloads |
| Info-stealer | Harvests credentials, cookies, and personal data (related to Stealer Logs) |
| Worm | Self-propagates across networks without user interaction |
| Rootkit | Hides malware presence by modifying the operating system |
| Exploit Kit | Automates exploitation of browser and plugin vulnerabilities |
Related
- Threat Actors -- Groups that deploy these malware families
- Indicators of Compromise -- Search for IOCs associated with specific malware
- Ransomware -- Dedicated tracking for ransomware groups and victims
- Campaigns -- Operations in which malware families are observed
- Compromised Users (Stealer Logs) -- Impact of info-stealer malware on your organization
