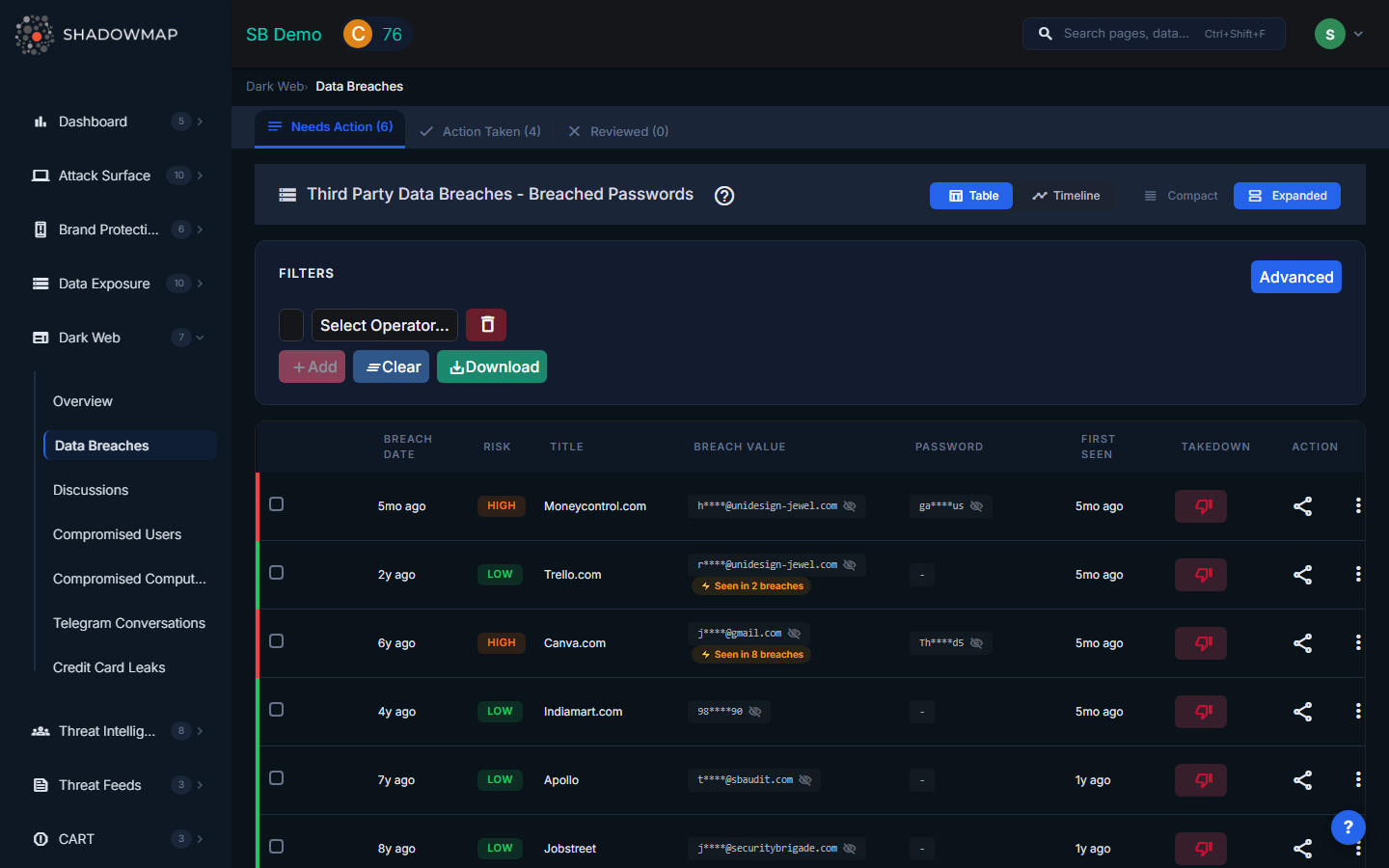
Data Breaches
ShadowMap monitors dark web sources for data breach dumps that contain information associated with your organization. When a third-party service is breached, employee or customer credentials may appear in dumps shared on forums, marketplaces, and paste sites. This view tracks all known breaches affecting your organization so you can respond before attackers exploit the exposed data.
Overview
View Modes
The page supports two view modes, toggled via the header:
- Table View -- Traditional sortable table with columns for bulk triage. Best for processing large volumes.
- Timeline View -- Chronological visualization of breaches showing when each breach occurred and was discovered. Best for identifying patterns and reporting.
Understanding the Data
| Column | Description |
|---|---|
| Breach Date | When the breach originally occurred at the third-party service |
| Risk | Severity rating based on data types exposed and credential freshness |
| Title | Name of the data breach or the breached service |
| Breach Value | The exposed credential or data point (email, username) belonging to your organization |
| Password | Whether a password was included in the breach data (plaintext, hashed, or not available) |
| First Seen | When ShadowMap first detected this data in dark web sources |
| Takedown | Takedown request status (if applicable) |
| Action | Current workflow status (Needs Action, Action Taken, False Positive) |
Filters
- Full-text search -- Search by breach name, email, domain, or other keywords
- Category filters -- Filter by risk level, source, data type, or date range
- Export -- Download filtered results in Excel format
How This Differs from Stealer Logs
| Factor | Data Breach | Stealer Log |
|---|---|---|
| Source | Third-party service was breached | User's device was infected with malware |
| Scope | One breached service per entry | Every service the user accessed |
| Password state | Often hashed or salted | Always plaintext |
| Freshness | Can be months or years old | Days to weeks old |
| Session cookies | Not included | Included -- can bypass MFA |
| Device context | No machine info | Full machine fingerprint |
Data breaches are important but generally lower urgency than stealer logs. Breached passwords may already be rotated, while stealer log credentials are typically recent and plaintext.
Recommended Actions
When New Breach Data Appears
- Identify affected users -- Cross-reference breached emails with your employee directory and SSO provider
- Force password resets -- Require password changes for all affected accounts, prioritizing accounts where the breach includes plaintext or weakly-hashed passwords
- Enable MFA -- If not already enforced, enable multi-factor authentication on all critical systems. Breach data makes credential stuffing trivial.
- Monitor for credential stuffing -- Check authentication logs for login attempts from unusual IPs or geolocations targeting affected accounts
- Notify affected individuals -- Follow your incident response plan and regulatory requirements (GDPR, state breach notification laws)
Ongoing Hygiene
- Set up SLA Policies to enforce response timeframes for new breach findings
- Review breach data regularly to identify employees who appear in multiple breaches (indicating password reuse)
- Use breach data to justify security awareness training focused on password hygiene and password manager adoption
Related
- Compromised Users (Stealer Logs) -- More urgent: credentials from infected devices
- Compromised Computers -- Machines identified in stealer log infections
- Leaked Credentials -- Credentials from public internet sources
- Dark Web Overview -- Summary of all dark web findings
- SLA Policies -- Automated response workflows for new findings
