Domains
The Domains view displays every root domain ShadowMap monitors for your organization. Each domain is the anchor point for a tree of subdomains, IP addresses, web applications, and security findings. Keeping this list accurate and up to date is essential -- an untracked domain is an unprotected domain.
Overview
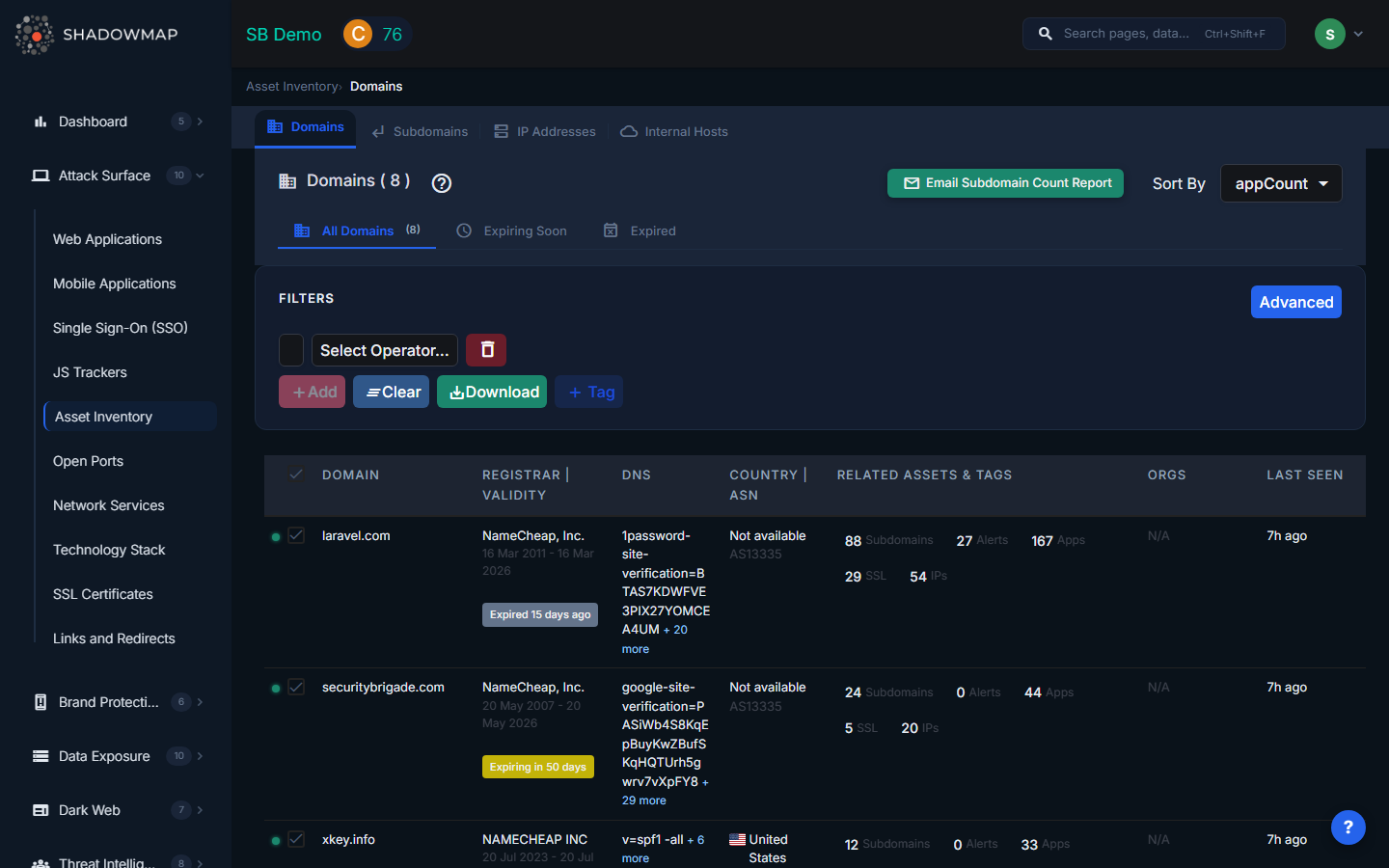
The table lists all domains with sortable columns, inline status indicators, and expandable detail rows.
| Column | Description |
|---|---|
| Domain | The root domain name (e.g., example.com) |
| Status | Online or Offline, based on the most recent scan |
| Organizations | Business units or entities associated with this domain |
| Subdomains | Count of discovered subdomains under this domain |
| IP Addresses | Count of unique IPs resolving from this domain's assets |
| Apps | Number of web applications detected on this domain |
| Alerts | Number of open security findings tied to this domain |
| SSL Certificates | Count of SSL/TLS certificates issued for this domain |
| Registrar | Domain registrar (e.g., GoDaddy, Namecheap, Cloudflare) |
| Registered Date | When the domain was originally registered |
| Expiry Date | When the domain registration expires |
| Country | Country associated with the domain's registration or hosting |
| ASN | Autonomous System Number for the domain's primary IP |
| Custom Tags | User-defined labels for organizing domains by business context |
| Last Seen On | Date of the most recent successful scan |
Filters
Use the filter bar to narrow down your domain list by:
- Domain Name -- search by full or partial domain name
- Status -- Online or Offline
- Country -- filter by hosting country
- ASN -- filter by autonomous system number
- Domain Validity -- Valid, Expired, Expiring Soon, or No Expiry Date
- Custom Tags -- filter by any user-defined tag values
Filters combine with AND logic. Your active filter state is preserved when exporting.
Domain Detail View
Click any domain to expand its inline detail, which surfaces critical registration health indicators:
- Is Expired -- whether the domain registration has lapsed (red if true)
- Is Multilocked -- whether the domain has multiple registrar locks enabled (green if true, indicating good security posture)
- Lock Effectiveness -- qualitative rating of the domain's transfer protection (red for "Very Low", amber for "Low")
- Is Redacted -- whether WHOIS privacy protection is active (green if true)
DNS Records
The detail view displays current DNS records grouped by type (A, AAAA, MX, NS, TXT, CNAME), showing only the most recent records when history exists. This helps you verify that DNS is configured correctly and detect unauthorized changes.
WHOIS Information
Registrar details, name servers (NS1, NS2), registration and expiry dates are pulled from WHOIS lookups and displayed alongside the domain. This data feeds the Domain Validity filter, enabling you to quickly find domains that need renewal.
Domain Expiry Monitoring
Expired or soon-to-expire domains pose a serious risk. An attacker who registers your lapsed domain inherits all traffic directed to it -- email, web requests, API calls -- and can impersonate your organization. ShadowMap categorizes domain validity into four states:
| State | Meaning |
|---|---|
| Valid | Expiry date is more than 100 days away |
| Expiring Soon | Expiry date is within the next 100 days |
| Expired | Expiry date has passed |
| No Expiry Date | WHOIS data does not include an expiry date (common with some ccTLDs) |
Use the Domain Validity filter to isolate domains that need attention.
Custom Tags
You can apply custom tags to domains to add business context that ShadowMap cannot infer automatically -- for example, tagging domains by business unit, acquisition date, or compliance scope. Tags are searchable and appear in exports.
Export
Click Export to download a CSV containing all visible columns plus DNS records, name servers, custom tags, and organizations. The export respects your current filter state.
How Domains Connect to the Broader Attack Surface
Each domain is a starting point for discovery. ShadowMap uses your domain list to:
- Enumerate subdomains via DNS and CT logs
- Resolve subdomains to IP addresses
- Scan IPs for open ports and services
- Crawl web applications for technology fingerprinting
- Match detected technologies against CVE databases
Changes to your domain list -- adding a new domain or removing a decommissioned one -- cascade through the entire discovery pipeline.
Related
- Subdomains -- subdomains discovered under your domains
- IP Addresses -- IPs associated with your domains
- Web Applications -- apps hosted on your domains
- SSL Certificates -- certificates issued to your domains
- Alerts -- security findings tied to your domains
