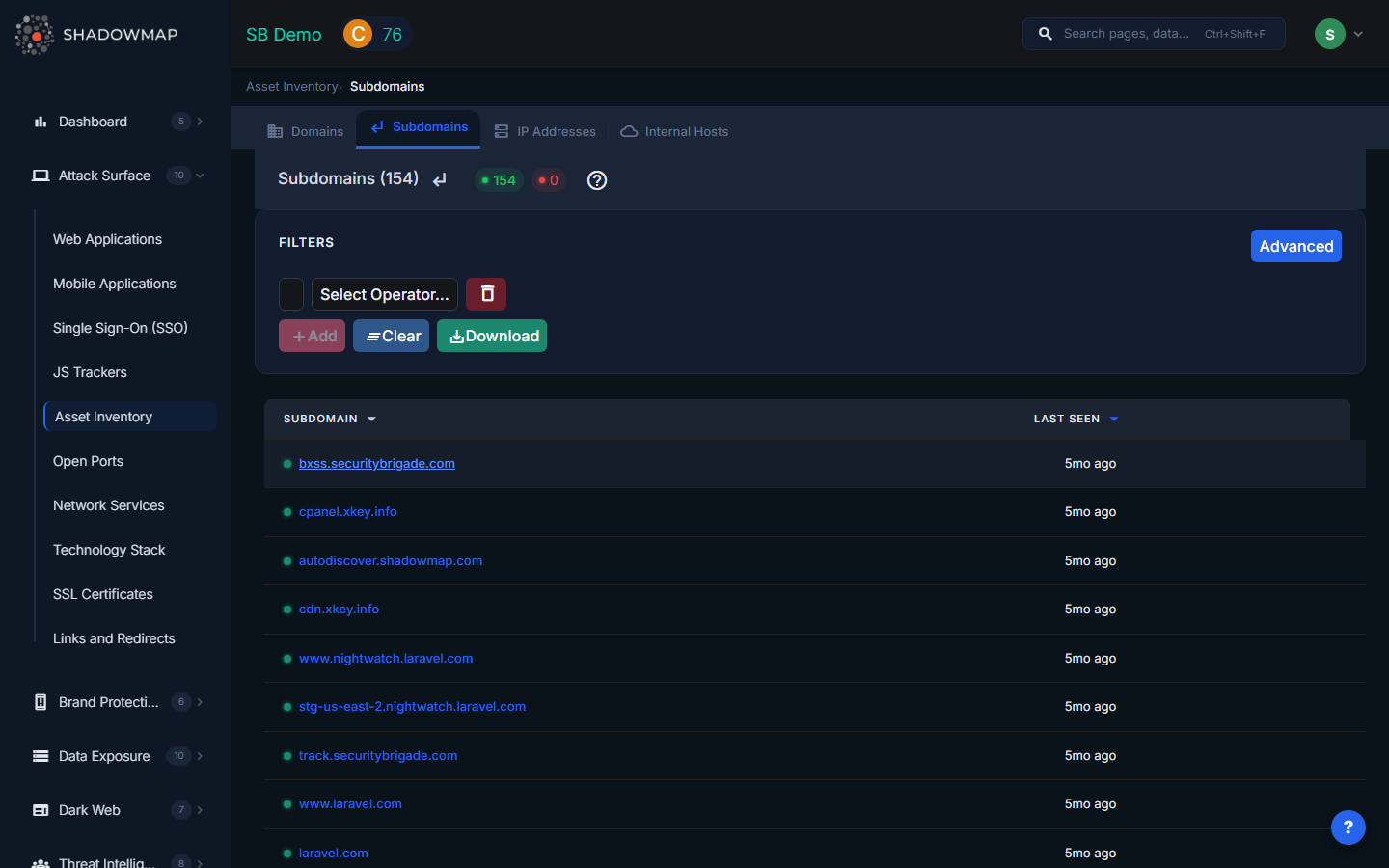
Subdomains
The Subdomains view lists every subdomain ShadowMap has discovered across your entire domain portfolio. Subdomains are where the real attack surface lives -- each one is a potential entry point that may host applications, expose services, or be vulnerable to takeover.
Overview
ShadowMap continuously discovers subdomains using DNS enumeration, Certificate Transparency log monitoring, and web crawling. New subdomains are typically detected within hours of creation.
| Column | Description |
|---|---|
| Subdomain | The fully qualified subdomain name (e.g., staging.api.example.com) |
| Status | Online or Offline, based on whether the subdomain currently resolves and responds |
| IP Address | The IP address the subdomain resolves to (via DNS A record) |
| Organization | The entity associated with this subdomain's hosting |
| Country | Geographic location of the hosting infrastructure |
| City | City-level geolocation |
| Provider | ASN provider / hosting company (e.g., AWS, Cloudflare, DigitalOcean) |
| First Seen On | When ShadowMap first discovered this subdomain |
| Last Seen On | The most recent scan that confirmed this subdomain exists |
Filters
Narrow down your subdomain list using the filter bar:
- Subdomain -- search by full or partial name
- IP Address -- filter by resolved IP
- Status -- Online or Offline
- Country -- filter by hosting country
- City -- filter by hosting city
- Provider -- filter by ASN / hosting provider
Combining filters lets you answer questions like "show me all offline subdomains hosted outside our primary cloud provider" -- a common indicator of shadow IT or decommissioned infrastructure.
Why Subdomain Monitoring Matters
Subdomains are the most dynamic part of your attack surface. Development teams create them for staging environments, QA testing, API endpoints, and microservices -- often without informing the security team. Each unmonitored subdomain is a potential risk.
Subdomain Takeover
When a subdomain's DNS record points to a cloud service (S3 bucket, Azure App Service, Heroku, etc.) that has been decommissioned, an attacker can claim that service and serve content under your domain. This is one of the most common attack vectors in EASM. Signs to watch for:
- Subdomains with Offline status that still have DNS CNAME records pointing to cloud providers
- Subdomains where the Provider is a cloud platform but no application responds
Forgotten and Stale Subdomains
Subdomains created months or years ago for one-off projects often run outdated software with known vulnerabilities. Use the First Seen On date to identify long-lived subdomains, then cross-reference with the Alerts module to check for unresolved findings.
Shadow IT Discovery
When business units provision infrastructure without going through official channels, those assets still appear in DNS. ShadowMap's continuous discovery catches these automatically. Look for subdomains with unfamiliar naming patterns or hosted on providers your organization does not officially use.
Development and Staging Exposure
Subdomains like dev., staging., test., uat., and internal. frequently expose sensitive data, debug endpoints, or admin panels. These should either be restricted by IP allowlist or taken offline entirely.
Subdomain Detail View
Click any subdomain to view its detail page, which aggregates everything ShadowMap knows about that asset:
Applications
Web applications hosted on this subdomain, including their technology stack, HTTP status, and risk rating.
Open Ports
If the subdomain resolves to an IP address, the detail view shows all open ports detected on that IP, including service name, product, version, CPE identifier, and banner data.
Alert Summary
A breakdown of security findings tied to this subdomain, categorized by severity (High, Medium, Low, Informational). This gives you an at-a-glance risk assessment without leaving the asset view.
Stealer Logs
If this subdomain appears in info-stealer malware logs, matching entries are shown here. This indicates that credentials for applications on this subdomain have been harvested by malware.
Data Breaches
Breach records where the affected domain matches this subdomain's base domain. Helps identify whether credentials associated with this asset have been exposed in known breaches.
Threat Exposure
Based on the technology stack detected on this subdomain (via its IP), ShadowMap correlates against the CVE database to show relevant vulnerabilities, including CVSS scores, KEV (Known Exploited Vulnerability) flags, and linked threat actors.
Export
Click Export to download a CSV of all subdomains matching your current filters. The export includes subdomain name, status, and last seen date.
Related
- Domains -- the root domains these subdomains belong to
- IP Addresses -- the IPs these subdomains resolve to
- Web Applications -- applications hosted on your subdomains
- Alerts -- security findings associated with your subdomains
- Stealer Logs -- compromised credentials matching your subdomains
- Data Breaches -- breach data involving your domains
