Ransomware
ShadowMap tracks ransomware groups, their encryption and payment methods, recent victims, and industry targeting patterns. Ransomware remains one of the most impactful cyber threats -- this module provides the intelligence your team needs to understand which groups are active, whether your industry is being targeted, and what TTPs to defend against.
Overview
Understanding the Data
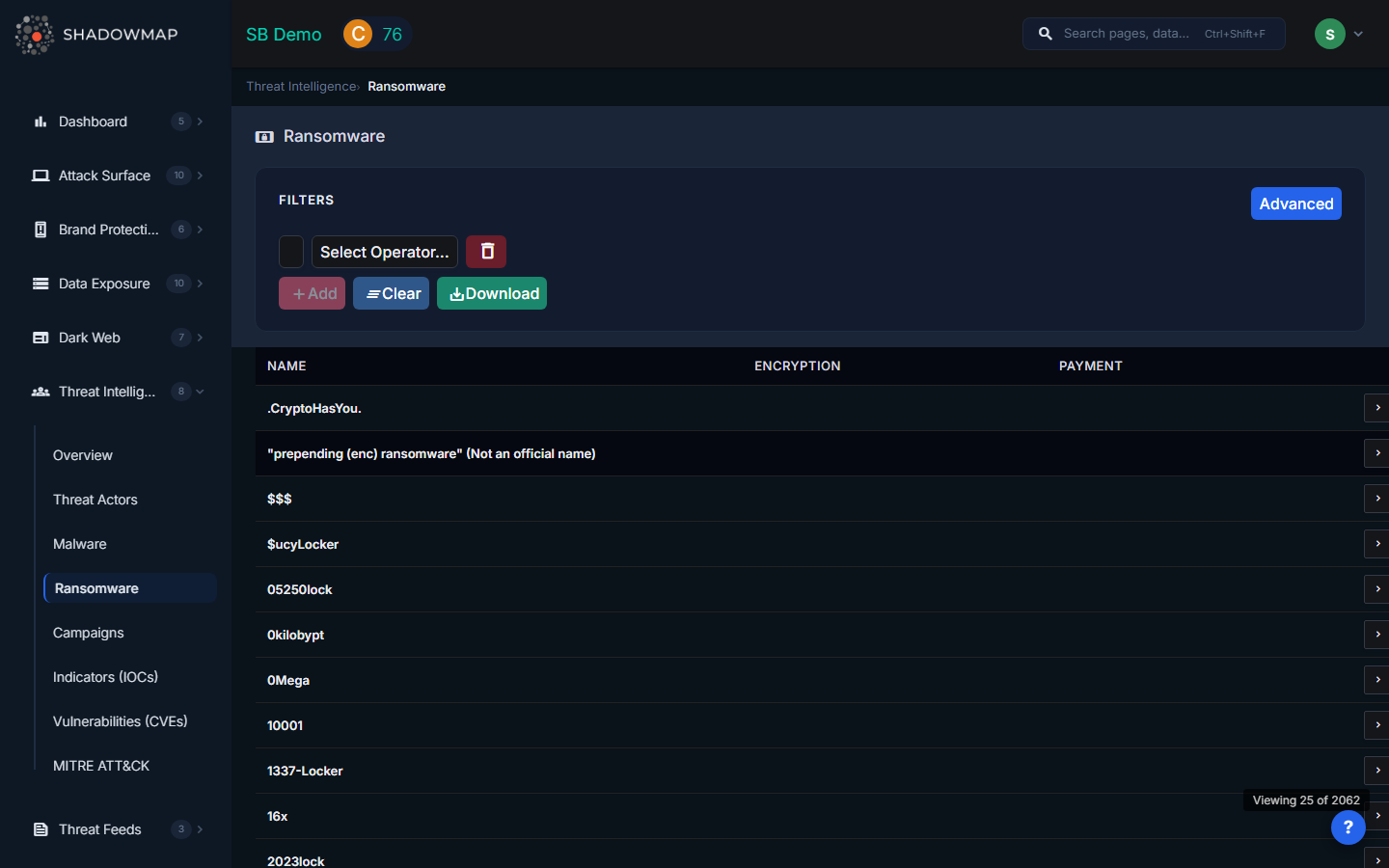
The ransomware list displays the following columns:
| Column | Description |
|---|---|
| Name | Primary name of the ransomware group or family (e.g., LockBit, BlackCat/ALPHV, Cl0p, Royal) |
| Encryption | Encryption method used by the ransomware (e.g., AES-256, RSA-2048, ChaCha20) |
| Payment | Ransom payment method (typically cryptocurrency: Bitcoin, Monero, or both) |
Click any row to view the full ransomware profile, including detailed descriptions, known TTPs, associated threat actors, recent victims, and related intelligence.
Filters
Use the filter bar to narrow the list:
| Filter | Options |
|---|---|
| Encryption | Filter by encryption algorithm used |
| Payment Method | Filter by ransom payment method |
| Search | Free-text search across ransomware names and descriptions |
Export
Click the export button to download the current filtered view as an Excel file.
Why Ransomware Intelligence Matters
Assess Your Risk
Ransomware groups increasingly specialize by industry. By tracking which groups are actively targeting your sector, you can:
- Prioritize patching and hardening for the initial access methods those groups prefer
- Brief leadership with concrete data about the threat landscape
- Justify security investments with evidence of sector-specific targeting
Understand TTPs
Each ransomware group has preferred initial access methods, lateral movement techniques, and data exfiltration procedures. Common patterns include:
- Initial access -- Exploiting VPN/firewall CVEs, phishing with malicious documents, purchasing access from initial access brokers
- Lateral movement -- RDP pivoting, credential dumping, Active Directory exploitation
- Data exfiltration -- Uploading data to cloud storage before encryption (double extortion)
- Encryption -- File-level encryption with per-file keys, volume shadow copy deletion, targeting backup systems
Monitor Victim Postings
Ransomware groups operate leak sites where they announce victims and publish stolen data when ransoms are not paid. ShadowMap monitors these announcements so you can:
- Identify when organizations in your supply chain are victimized
- Track industry targeting trends over time
- Detect if your own organization appears as a victim
Prepare Response Plans
Use ransomware intelligence to build incident response playbooks:
- Map each ransomware group's TTPs to your detection coverage
- Pre-position decryption tools where available
- Establish communication channels with law enforcement contacts
- Document decision trees for ransom payment scenarios
Connection to Other Modules
| Module | Relationship |
|---|---|
| CVEs | The "RW" column flags CVEs known to be exploited by ransomware groups |
| Threat Actors | Many ransomware groups overlap with or are operated by tracked threat actors |
| MITRE ATT&CK | Ransomware TTPs map to specific ATT&CK techniques for detection planning |
| Campaigns | Major ransomware operations appear as tracked campaigns |
| Dark Web Discussions | Ransomware group activity often surfaces in dark web forums |
Related
- Threat Actors -- Groups behind ransomware operations
- Malware -- Technical capabilities of ransomware payloads
- Campaigns -- Ransomware operations as tracked campaigns
- Vulnerabilities (CVEs) -- CVEs exploited by ransomware groups
- Threat Intelligence Overview -- Summary dashboard
