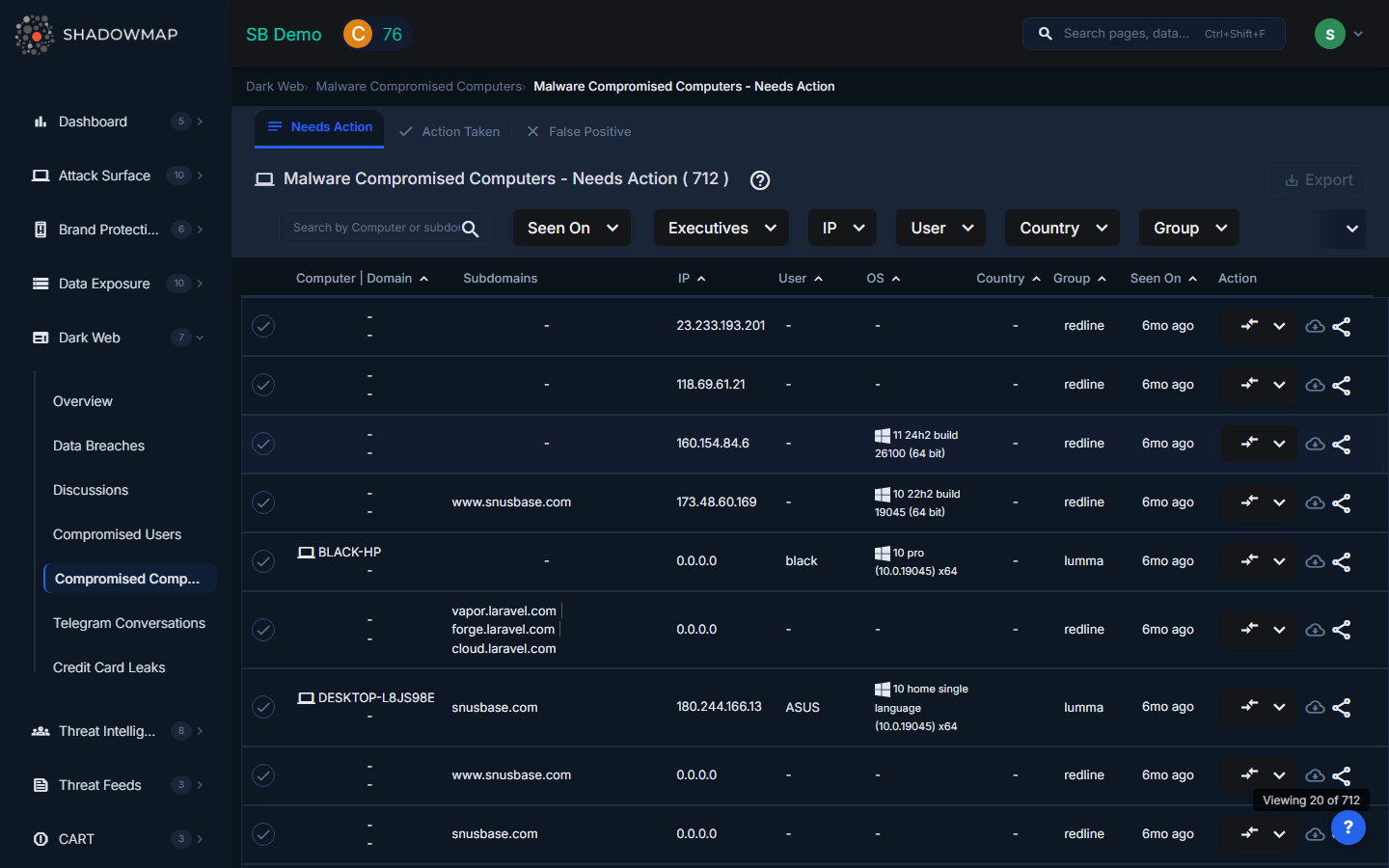
Compromised Computers
ShadowMap identifies corporate machines that appear in stealer log data, indicating active or recent malware infections on your network. This view presents the same stealer log intelligence as Compromised Users, but aggregated by machine rather than by user -- helping you identify infected endpoints and scope the remediation effort.
Overview
Understanding the Data
Each entry represents a unique machine identified in stealer logs. The data comes from info-stealer malware (Redline, Raccoon, Vidar, Lumma, etc.) that fingerprints the infected device alongside the stolen credentials.
| Field | Description |
|---|---|
| Computer Name | Machine hostname or hardware fingerprint extracted from the stealer log |
| Subdomain | The corporate subdomain associated with the stolen credentials |
| Credential Count | Number of credentials harvested from this machine -- higher counts indicate the user had saved passwords for many services |
| Stealer Family | The malware variant that infected the machine (e.g., Redline, Raccoon, Vidar, Lumma) |
| IP Address | The machine's IP address at the time of infection |
| Executives | Whether the compromised user is flagged as an executive |
| First/Last Seen | When the stealer log data was first and most recently observed in dark web sources |
Filters
- Search -- Filter by computer name or subdomain
- Date range -- Filter by when the stealer log was seen
- Executives -- Show only machines used by executives
- IP -- Filter by specific IP addresses
- Stealer Family -- Filter by malware variant
Actions
- Workflow status -- Mark findings as Action Taken, False Positive, or revert to Needs Action
- Bulk actions -- Select multiple machines and change status in batch
- Share via Integration -- Push to your ticketing system, SIEM, or messaging platform
- Export -- Download filtered results as CSV
Incident Response Playbook
Phase 1: Immediate Containment
- Isolate the affected machine from the network immediately. Do not simply disconnect -- use your EDR or MDM to enforce network quarantine so the device cannot communicate laterally or with C2 servers.
- Revoke all sessions for every user who logged into this machine. Info-stealers capture session cookies that bypass MFA.
- Reset all credentials that were used on the machine. The stealer log captures every saved password in every browser -- check the corresponding Compromised Users entries for the full list.
Phase 2: Investigation
- Identify the infection vector -- Check email logs, download history, and EDR alerts around the first-seen date. Common vectors: phishing emails with malicious attachments, drive-by downloads, cracked software.
- Scope the blast radius -- Were any shared credentials (admin accounts, service accounts) used on this machine? Check if other machines in the same network segment show similar indicators.
- Review access logs -- Search your SIEM for the machine's hostname and IP to identify any lateral movement or data exfiltration.
Phase 3: Remediation
- Re-image the device -- Stealer malware often includes persistence mechanisms. Do not attempt to clean -- re-image from a known-good baseline.
- Audit connected services -- For each URL in the stealer log, verify whether unauthorized access occurred.
- Reset API keys and tokens -- Any secrets accessible from the compromised device should be rotated.
Phase 4: Prevention
- Deploy EDR with behavioral detection for info-stealer malware families
- Enforce password manager usage -- Discourage saving passwords in browsers
- Monitor for recurrence -- Configure SLA Policies for immediate escalation on new compromised computer findings
Relationship to Compromised Users
| View | Grouped By | Best For |
|---|---|---|
| Compromised Users | Email/username | Identifying which people are affected and resetting their credentials |
| Compromised Computers | Machine identifier | Identifying which devices need to be isolated and re-imaged |
Both views draw from the same underlying stealer log data. Use Compromised Users for credential response and Compromised Computers for endpoint response.
Related
- Compromised Users (Stealer Logs) -- Same data, grouped by user
- Data Breaches -- Third-party breach data (lower urgency than stealer logs)
- Dark Web Overview -- Summary of all dark web findings
- SLA Policies -- Automated response workflows for new findings
