IP Addresses
The IP Addresses view provides a complete inventory of every IP address associated with your organization's external infrastructure. IP addresses are the lowest-level asset in the attack surface hierarchy -- they host your services, expose your ports, and are what attackers ultimately target.
Overview
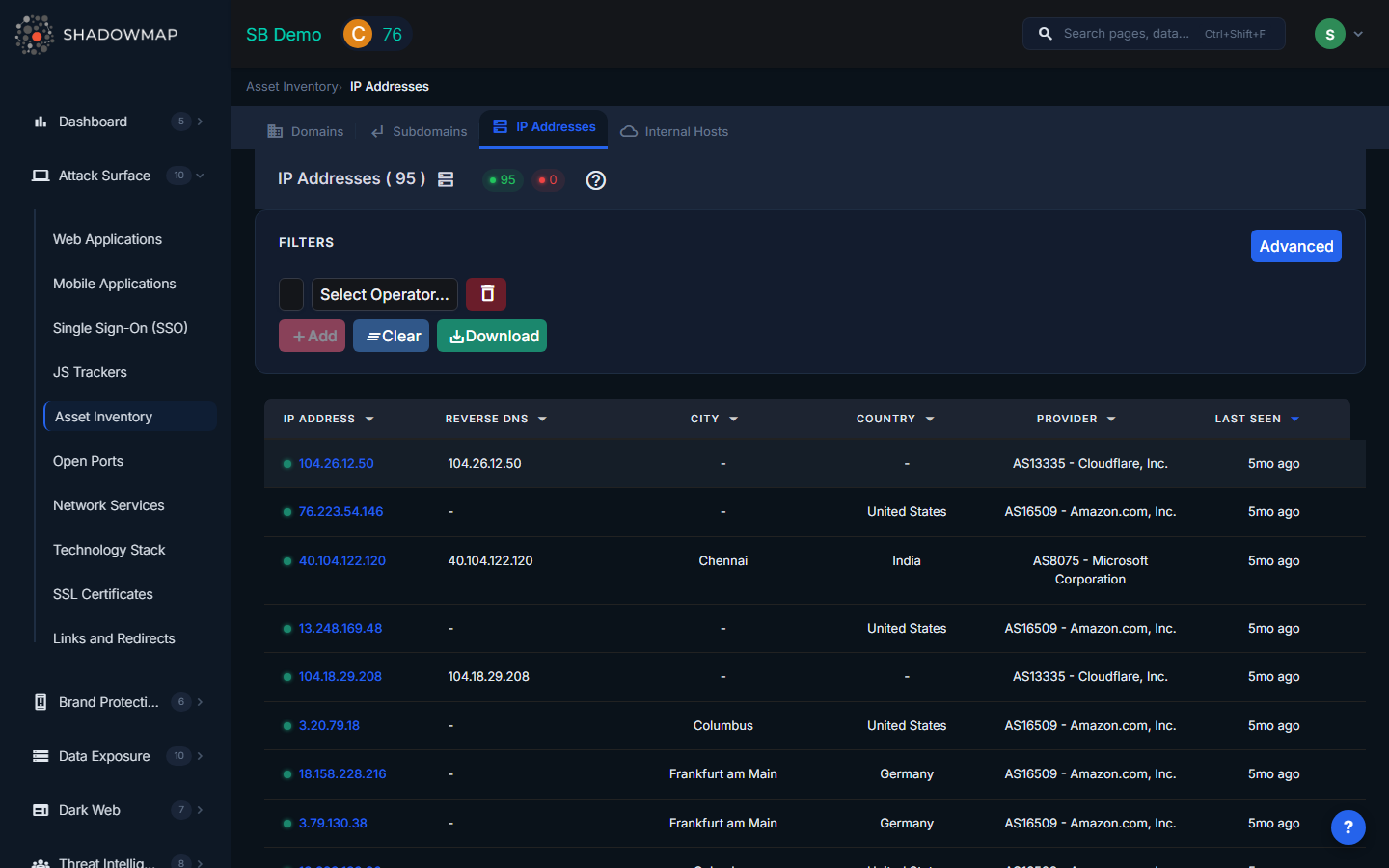
The table lists all discovered IP addresses with sortable columns and expandable detail rows.
| Column | Description |
|---|---|
| IP Address | The IPv4 or IPv6 address |
| Status | Online or Offline, based on the most recent scan |
| Reverse DNS | The PTR record hostname, if one exists |
| City | City-level geolocation of the IP |
| Country | Country where the IP is geographically located |
| Provider | ASN provider or hosting organization (e.g., Amazon, Cloudflare, Hetzner) |
| Last Seen On | Date of the most recent successful scan |
CDN Detection
Expanding an IP row reveals whether ShadowMap has identified it as a CDN (Content Delivery Network) address. CDN IPs are typically shared infrastructure (Cloudflare, Akamai, Fastly) and behave differently from dedicated hosting -- they may serve multiple tenants and their open ports reflect the CDN provider, not your specific configuration. Knowing which IPs are CDN-fronted helps you prioritize scanning effort on your directly-hosted infrastructure.
Filters
Use the filter bar to focus on specific segments of your IP inventory:
- IP Address -- search by full or partial IP
- Reverse DNS -- filter by PTR record hostname
- Status -- Online or Offline
- Country -- filter by geolocation country
- City -- filter by geolocation city
- Provider -- filter by ASN provider / hosting company
These filters support use cases like "show me all IPs hosted outside our approved regions" for compliance audits, or "show me all IPs from a specific cloud provider" for infrastructure reviews.
IP Address Detail View
Click any IP to open its detail page, which consolidates all intelligence ShadowMap has gathered about that address.
Open Ports and Services
A full listing of every open port detected on this IP, including:
- Port number -- the TCP/UDP port
- Service -- the protocol or service type (HTTP, SSH, SMTP, etc.)
- Product -- the specific software serving on this port (nginx, OpenSSH, etc.)
- Version -- the detected software version
- CPE -- Common Platform Enumeration identifier for precise vulnerability matching
- Banner -- raw service banner text, useful for manual analysis
Ports are ordered numerically. This data feeds directly into threat exposure analysis.
Associated Subdomains
All subdomains from your inventory that resolve to this IP address, with their status and last seen date. This reveals IP-to-hostname relationships and helps you understand what is actually running on each address. A single IP may host dozens of subdomains via virtual hosting.
Web Applications
Applications discovered on this IP, showing host, port, protocol, risk level, and scan history. Cross-references with the Web Applications module for full detail.
SSL Certificates
SSL/TLS certificates served by applications on this IP, including subject name, validity period (valid from / valid until), and the host and port where each certificate was observed. Expired or misconfigured certificates on your IPs are a common source of security alerts.
Alert Summary
A severity breakdown of all security findings (High, Medium, Low, Informational) associated with this IP across all ShadowMap scan modules. The alert tab provides detailed alert listings with title, host, port, risk level, status, and timestamps.
Threat Exposure
ShadowMap correlates the technology stack detected on this IP (from both application fingerprinting and port service detection) against the global CVE database. The threat exposure section shows:
- Technology stack -- all detected products with version and source (Application or Network layer)
- Matched CVEs -- vulnerabilities affecting your detected technologies, ranked by CVSS score
- KEV flags -- which CVEs appear in CISA's Known Exploited Vulnerabilities catalog
- Linked threat actors -- APT groups and threat actors known to exploit these CVEs, sourced from MISP threat intelligence
This gives you a direct line from "what is running on this IP" to "who might target it and how."
Connection to IP Reputation
IP addresses in your inventory are also evaluated by the IP Reputation module, which checks your IPs against blocklists, abuse databases, and threat intelligence feeds. An IP appearing on a blocklist may indicate compromise, spam relay, or prior malicious activity. Use both views together: the Asset Inventory shows what is running on the IP, while IP Reputation shows how the rest of the internet perceives it.
Export
Click Export to download a CSV of all IP addresses matching your current filters. The export includes IP address, status, reverse DNS, city, country, provider, and last seen date.
Common Use Cases
- Compliance audit -- filter by country to verify all IPs are hosted in approved jurisdictions
- Cloud migration tracking -- filter by provider to see which IPs remain on legacy hosting
- Incident response -- use the detail view to quickly assess what an attacker-targeted IP exposes
- Vulnerability prioritization -- check threat exposure to find IPs running software with critical CVEs
Related
- Domains -- the domains whose subdomains resolve to these IPs
- Subdomains -- subdomains hosted on these IPs
- Web Applications -- applications running on these IPs
- IP Reputation -- blocklist and reputation data for your IPs
- Alerts -- security findings associated with these IPs
- Vulnerability Overview -- CVE tracking across your infrastructure
