Dark Web Overview
The Dark Web module monitors underground forums, marketplaces, stealer log repositories, Telegram channels, and breach dumps for mentions of your organization. It surfaces compromised credentials, data breaches, threat actor discussions, and payment card leaks -- giving your security team early warning of threats that originate outside your perimeter.
Overview
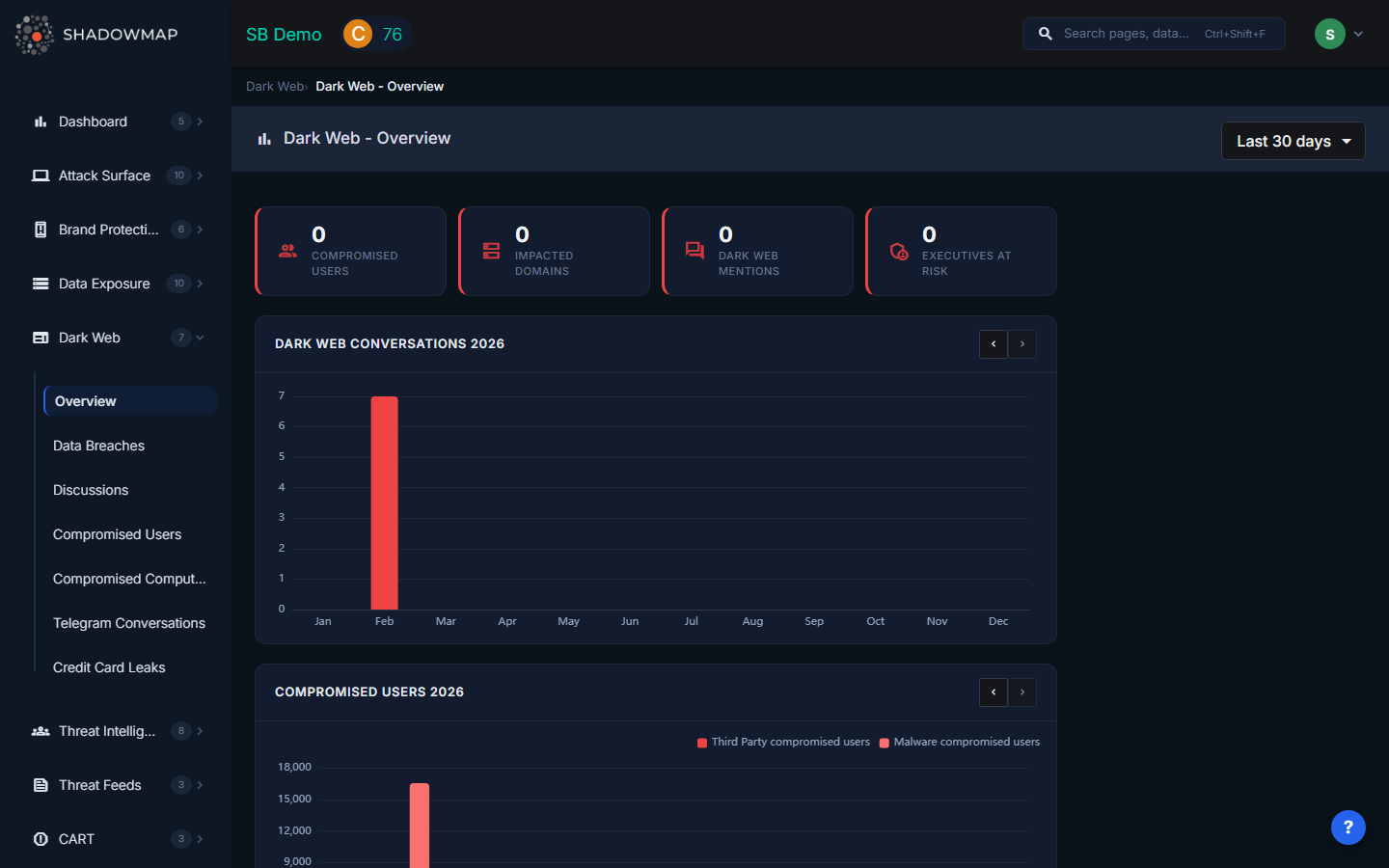
Hero Metrics
The top of the dashboard displays four summary cards:
| Metric | What It Measures |
|---|---|
| Compromised Users | Total count of employee credentials found across stealer logs and breach data |
| Impacted Domains | Number of your domains and subdomains that appear in dark web findings |
| Dark Web Mentions | Total mentions of your organization across forums, Telegram, and other channels |
| Executives at Risk | Count of executive-level personnel whose data appears in dark web sources |
Dashboard Sections
Trend Charts
Two side-by-side bar charts show monthly volumes with year-over-year navigation:
- Dark Web Conversations -- Monthly count of forum posts and Telegram messages mentioning your organization. A spike may indicate a coordinated campaign or new interest from threat actors.
- Compromised Users -- Monthly count of new stealer log credentials discovered. Rising trends suggest ongoing infections within your employee base.
Most Impacted Domains & Subdomains
A multi-column breakdown showing which of your domains and subdomains appear most frequently in dark web data, organized by module (Stealer Logs, Data Breaches, Discussions, etc.). Toggle between All Domains and Priority to focus on high-value assets.
Most Impacted Users
Shows the employees whose credentials appear most frequently across dark web sources, broken out by module. High counts for a single user may indicate persistent device compromise.
Most Impacted Executives
Same format as impacted users, but filtered to executives configured in your organization's executive monitoring settings.
Activity Feed
A sidebar feed shows recent dark web findings in chronological order with severity indicators and source attribution.
Date Range Filter
Use the dropdown in the page header to adjust the time window: Today, Last 7 Days, Last 30 Days (default), or This Year.
Data Sources
ShadowMap collects dark web intelligence from:
- Underground forums and marketplaces -- Hacking forums, carding shops, and access brokers
- Data breach dumps and paste sites -- Public and private dump repositories
- Stealer log repositories -- Redline, Raccoon, Vidar, Lumma, and other info-stealer output
- Telegram channels and groups -- Threat actor communication channels
- Onion sites and hidden services -- Tor-based marketplaces and leak sites
Modules
| Module | Description |
|---|---|
| Data Breaches | Your organization's data found in dark web breach dumps |
| Compromised Users | Employee credentials harvested by info-stealer malware |
| Discussions | Dark web forum posts mentioning your organization |
| Compromised Computers | Corporate machines identified in stealer log data |
| Telegram Conversations | Threat actor communications on Telegram mentioning your brand |
| Credit Card Leaks | Payment card data associated with your organization |
Related
- Dashboard Overview -- Organization-wide security posture
- Data Exposure Overview -- Publicly exposed data on the open internet
- Leaked Credentials -- Credentials found on public sources (distinct from dark web)
- Security Rating -- Dark web findings affect your Dark Web & Threat Intelligence category score
